Technology
MataRecycler Waste Management with AI-Powered Recycling
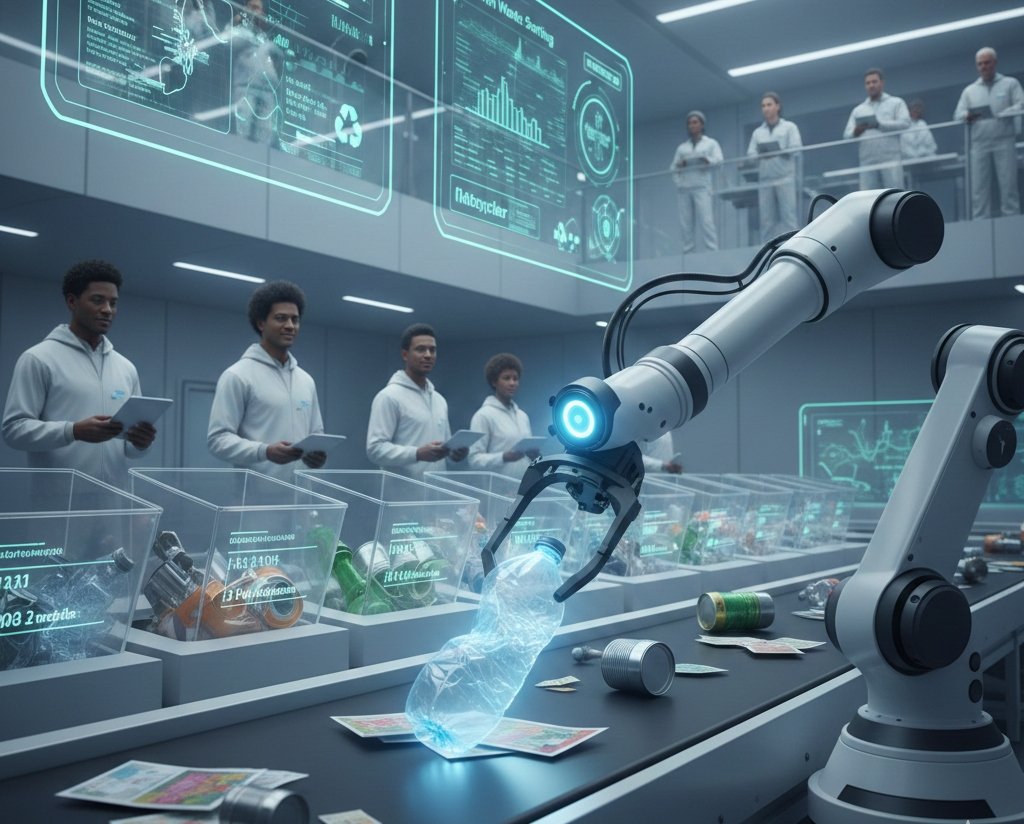
Artificial Intelligence (AI) is transforming physical infrastructure, and MataRecycler is a smart recycling system that uses AI, sensors, and data analytics to identify recyclable materials and reduce contamination. This system operates as an integrated platform connecting smart bins with computer vision and machine learning models to improve waste sorting at scale. The main benefits of MataRecycler include higher material recovery rates, lower operational costs for municipalities, and measurable impact for sustainability commitments. Its primary applications span across cities, residential areas, and commercial facilities to manage plastic, paper, metals, and food waste. The system consists of three main components: a smart collection system with fill-level sensors, an intelligent sorting system using optical scanners, and a cloud-based data analytics platform.
What Is MataRecycler?
MataRecycler is an AI-driven waste sorting platform designed to automate the identification and separation of recyclable materials. It is not just a single piece of hardware but a comprehensive material recovery system that integrates computer vision, machine learning models, and robotics. By analyzing the shape, texture, and color variation of items in the waste stream, MataRecycler helps facility operators achieve higher accuracy because the system evaluates patterns rather than simple identifiers.
Why Traditional Recycling Needs Improvement
Traditional recycling systems are reaching their limits because they rely on rigid rules and manual sorters. There are 5 primary reasons why these older systems struggle:
-
High contamination rates from food waste or mixed materials.
-
Manual sorting costs that increase operational expenses for municipalities.
-
Inability to adapt to new packaging formats like multi-layer films.
-
Fixed collection routes that waste fuel and energy.
-
Limited data insights for recycling facility managers to optimize logistics.
How MataRecycler Works
MataRecycler works by treating waste as a data-rich problem through 3 integrated stages:
-
Detection: High-speed optical scanners and cameras capture images of the waste stream.
-
Analysis: The system uses computer vision and machine learning models to identify materials like plastic (PET, HDPE), metals, and paper.
-
Action: Once identified, mechanical actuators like air jets or magnets divert the item into the correct bin.
Each sorting decision feeds AI-generated data back into the model, creating a feedback loop that improves accuracy over time.
Key Features of the MataRecycler System
The MataRecycler system offers 6 core features that distinguish it from standard processing machinery:
-
AI-Driven Waste Sorting: Real-time identification of complex materials.
-
Smart Bins: Sensors that monitor fill levels (0-100%) to optimize collection timing.
-
Optical Scanners: Advanced sensors that detect material density and composition.
-
Cloud Analytics: Dashboard for cities to track recycling rates and error patterns.
-
Scalable Design: Modular units that fit into existing recycling facilities.
-
Reverse Logistics Support: Tools to help manage the return of materials into the circular economy.
Incentives and User Engagement
MataRecycler improves community participation by providing clear feedback and rewards. The system encourages correct disposal behavior through 4 main methods:
-
Reward points for users who recycle correctly at smart bins.
-
Digital badges that track a user’s carbon footprint reduction.
-
Real-time guidance on bin screens to reduce confusion (e.g., 9r recycle principles).
-
Community goals that unlock local environmental projects.
Environmental Impact and Sustainability Benefits
There are 4 major environmental benefits provided by MataRecycler:
-
Reduction in Landfill Dependency: Diverts up to 30% more waste than traditional methods.
-
Lower Carbon Footprint: Optimized routes reduce fuel consumption in waste logistics.
-
Resource Recovery: Increases the purity of recycled materials, supporting closed-loop recycling.
-
Urban Mining Support: Improves precious metal recovery from E-waste recycling and scrap metal recycling.
Role of Technology in MataRecycler’s Success
Technology is the core enabler of MataRecycler’s performance. Artificial Intelligence (AI) and Computer Vision (CV) allow the system to learn from complexity. Instead of needing manual recalibration for every new product launch, the AI-backed software updates its material definitions automatically. This level of smart automation ensures that recycling equipment manufacturers can offer systems that stay relevant as consumer behavior evolves.
Community Engagement and Awareness Programs
MataRecycler invests in education because technology requires human cooperation to succeed. There are 3 primary awareness initiatives:
-
Educational Workshops: Teaching the 4R materials (Reduce, Reuse, Recycle, Recover) in schools.
-
Pilot Programs: Deploying smart bins in high-traffic areas to gather user feedback.
-
Transparency Reports: Sharing data with the public to show the measurable impact of their recycling efforts.
Ethical and Environmental Considerations
MataRecycler addresses ethical concerns by focusing on workforce transition and data privacy.
-
Workforce Dimension: The system shifts manual sorters into higher-level oversight roles or system optimization tasks.
-
Data Security: All AI-generated data is anonymized to protect consumer privacy while maintaining operational transparency.
-
Sustainability Commitments: The system uses energy-efficient components to ensure the energy used for sorting does not outweigh the carbon saved.
Frequently Asked Questions
What are 3 recycled materials MataRecycler handles best?
MataRecycler handles 3 materials with high efficiency: plastic (specifically PET and HDPE), aluminum cans, and corrugated cardboard.
Does MataRecycler require high maintenance?
Yes, MataRecycler requires regular maintenance of its optical scanners and conveyor belts to ensure 99% accuracy. Most maintenance is predictive, based on real-time sensor data.
Can it be used for E-waste recycling?
Yes, MataRecycler can be configured for E-waste recycling and Lithium-ion battery recycling by using specialized sensors for precious metal recovery.
Who are the primary users of the system?
Municipalities, recycling facility managers, and large commercial enterprises are the primary users of the MataRecycler platform.
Is the system better than manual sorting?
Yes, AI-driven waste sorting is faster and more consistent than manual sorting, especially in high-volume recycling facilities.
Technology
Tracqueur What It Is, How It Works & Best Uses

A Tracqueur is a tracking device or software system used to monitor location, movement, or task progress in real time. It combines GPS technology, sensors, and digital dashboards to provide accurate data for vehicle tracking, asset security, personal safety, and productivity management. With benefits like improved efficiency, enhanced safety, and better time management, Tracqueurs are widely used across industries. Whether as a physical GPS tracker or a digital workflow tool, they help users stay informed, organized, and in control through real-time insights and smart data analysis.
A Tracqueur is a specialized tracking tool or digital platform used to monitor location, movement, and task progress in real time. It functions by gathering data through hardware sensors or software inputs and displaying that information on an intuitive dashboard. The main benefits of using a Tracqueur include improved safety, enhanced workforce efficiency, and better time management. These systems are used for GPS tracking, vehicle monitoring, asset recovery, and professional project management. The main parts of a physical Tracqueur include a GPS chip, a battery, an antenna, and a SIM card, while software versions consist of customizable task lists and analytics tools.
What Is a Tracqueur?
A Tracqueur (TQR) is a tracking device or software system designed to follow the location, movement, or activity of an object, person, or digital project. It acts as a smart locator that collects data and transmits it to a phone, app, or centralized task management system. While some models exist as physical hardware for GPS tracking, others function as productivity software for modern professionals.
The primary goal of any Tracqueur is to provide real-time monitoring and situational awareness. For a freelancer, it might be a tool to track progress seamlessly on a client project. For a logistics manager, it is a physical unit used for vehicle tracking to ensure delivery accuracy. Because of this versatility, the term applies to both the physical realm of security and the digital realm of project management.
What Does the Word Tracqueur Really Mean?
The word Tracqueur is derived from the French term for “tracker,” referring to an entity that follows clues or signals to monitor a target. In a modern context, it describes a gadget or software platform that watches and records data over time. It is a synonym for “traceur” or “balise de suivi.”
In the tech industry, a Tracqueur is often viewed as a comprehensive solution for organization. It signifies a shift from manual oversight to automated, continuous operational oversight. Whether it is a Petit tracqueur GPS for a pet or a complex workflow system for a startup, the meaning remains rooted in the ability to trace and retrieve information accurately.
How Does a Tracqueur Work?
A Tracqueur works by detecting position or task status, transmitting that data over a network, and displaying the results on a user interface. Most hardware devices rely on Global Positioning System (GPS) technology to calculate coordinates via satellites. Once the position is determined, the device sends data through GSM, Wi-Fi, or Bluetooth networks.
In a professional software environment, the process involves:
-
Data Input: Users or sensors log activities into a task management system.
-
Processing: The software uses a proprietary algorithm deployment to analyze productivity or location.
-
Visualization: An intuitive dashboard displays the information, allowing users to visualize tasks at a glance or see a dot on a map.
Types of Tracqueurs
There are 5 main types of Tracqueurs used across different industries, including:
-
GPS Trackers: These units focus on Vehicle Tracking and Asset Tracking for anti-theft and fleet management.
-
Personal Trackers: These are small devices used for Personal Tracking of children, elderly relatives, or solo travelers.
-
Pet Trackers: These attach to collars to help owners locate lost animals.
-
Productivity Trackers: These are software-based systems used by a marketing manager or a freelance graphic designer to manage your time.
-
Fitness Trackers: These wearable devices monitor health metrics and movement patterns.
Benefits of Using Tracqueur
The main benefit of using a Tracqueur is the provision of real-time tracking, which allows users to act immediately during emergencies or deadlines. There are 4 additional advantages to using these systems:
-
Improved Safety: Using a Tracqueur GPS moto or car unit provides precision asset recovery if theft occurs.
-
Increased Efficiency: Teams can allocate their hours better and prioritize their assignments using integrated analytics.
-
Reduced Stress: Knowing the location of a missing bag or the status of a project deadline tracking which keeps urgency in mind reduces anxiety.
-
Better Data Insights: Users can identify areas for improvement by reviewing movement history or performance metrics.
Why Are Tracqueurs Becoming So Popular Right Now?
Tracqueurs are becoming popular because mobile functionality and AI integration have made tracking more accessible and affordable. As remote work becomes a standard in many industries, modern professionals need tools that centralize workflow management.
Another reason for their rise is the “Marsh Magazine” effect—increased media coverage of success stories involving recovered assets or boosted productivity. Small, low-profile device placement and long battery life (Autonomie tracqueur GPS) have made these tools a practical choice for everyday people, not just tech experts.
What Makes a Good Tracqueur Helpful and Safe?
A good Tracqueur is characterized by high accuracy, long battery life, and strong data privacy protections. Accuracy is vital so that the device shows the correct spot or project status most of the time.
A reliable system should also include:
-
Intuitive Tracking Features: The interface should be easy to navigate without a steep learning curve.
-
Encrypted Communication: This prevents unauthorized parties from intercepting location or project data.
-
Customizable Notifications: Users should receive alerts for upcoming deadlines or unusual movement.
-
Durable Design: Hardware must be waterproof and shock-resistant for outdoor use.
How to Choose the Right Tracqueur
Choose the right Tracqueur by identifying your primary goal, such as vehicle security or personal productivity. If you need to manage a large team, look for a task management system with seamless integration with calendars and communication apps.
When selecting a hardware device, consider these 3 factors:
-
Network Support: Ensure the device works with local GSM or Wi-Fi signals.
-
Battery Cycle: Select a model with “Longue autonomie” to avoid frequent charging.
-
Subscription Costs: Check if the Tracqueur GPS sans abonnement (without subscription) fits your budget or if you prefer a premium monthly service.
FAQs
What is a Tracqueur used for?
A Tracqueur is used for monitoring the location of assets or the progress of professional tasks. It helps with safety, logistics, and time management.
Is using a Tracqueur legal?
Yes, using a Tracqueur is legal when tracking your own property or with the consent of the person being tracked. You should always check local privacy laws.
How accurate is GPS tracking?
GPS tracking is typically accurate within 3 to 10 meters (10 to 33 feet) in outdoor environments. Accuracy may decrease indoors or in dense urban areas.
Does a Tracqueur require the internet?
Yes, a Tracqueur usually requires internet or cellular network access to provide real-time updates to your phone or computer. Some models can store data offline and sync later.
How long does the battery last?
Battery life for a Tracqueur varies from 2 days to several months, depending on the model and the frequency of location updates. Smaller units often require more frequent charging.
Technology
Ausbeulstation The Future of Car Dent Repair

An Ausbeulstation is a modern dent repair workstation designed to streamline automotive body repair by integrating advanced tools into a single mobile unit. It enables technicians to perform precise, paintless dent removal using systems like SPEEDLINER PRO 400 and glue pulling tools, reducing repair time and costs while preserving the vehicle’s original paint. Compared to traditional methods, it is faster, less invasive, and more environmentally friendly due to lower emissions and reduced material waste. Widely used in professional auto body shops, Ausbeulstation technology represents the future of efficient, high-quality car dent repair, especially for modern materials like aluminum and electric vehicles.
An Ausbeulstation (dent repair station) is a specialized modular workstation designed to streamline the Karosserie Reparatur (body repair) process by integrating all necessary tools for dent removal into a single mobile unit. It works by providing technicians with immediate access to advanced pulling systems, welding units, and specialized hand tools, allowing for faster and more precise repairs on both steel and aluminum panels. There are 4 primary benefits of an ausbeulstation, including reduced repair times, improved precision, cost efficiency, and a smaller environmental footprint. These stations are mainly used in professional autowerkstatt (car repair shops) and karosseriewerkstatt (body shops) for tasks such as hail damage mitigation, park dent removal, and structural straightening. The main components of a high-end station include a power source like the SPEEDLINER PRO 400, a KLEBE PULLER SET, various pulling levers, and an Ausbeul Gleithammer Satz (slide hammer set).
The traditional process of car dent repair
The traditional process of karosserieinstandsetzung (bodywork restoration) often involves invasive methods that require stripping the vehicle’s interior and removing exterior paint. Technicians frequently use heavy hammers and dollies to manually beat the metal back into shape from the inside out. This approach increases labor hours because the technician must sand the damaged area, apply body filler, and perform a complete lackschadenreparatur (paint damage repair) to match the original factory finish. Because traditional methods are so labor-intensive, they often lead to longer vehicle downtime for the customer.
Ausbeulstation – the innovative solution
An ausbeulstation represents the innovative solution to these legacy inefficiencies by centralizing advanced Smart Repair technology. Manufacturers like GYS FRANCE (active since 1964) have pioneered units such as the SPEEDLINER PREMIUM PRO EXPERT 400 + ARCPULL 350 to handle complex Karosserie Reparatur. Unlike scattered toolboxes, these stations provide a dedicated environment for lackierfreien Ausbeulen (paintless dent removal) and specialized welding. GYS Deutschland and other international branches like GYS ITALIA, GYS UK, and GYS IBERICA distribute these systems to ensure global standards in invisible repair technology.
How does it work?
To use an ausbeulstation, a technician first identifies the material of the panel, such as steel or aluminum, to select the correct power settings.
-
Clean the surface to ensure maximum adhesion or electrical contact.
-
Attach the pulling element using either KLEBE PULLER SET tabs for lackschadenfreie Ausbeulstation Reparatur or by welding a stud with a unit like the PROLINER PRO 230.
-
Apply controlled tension using a bridge or a GLUE LIFTER to pull the metal back to its original position.
-
Finish the surface with an Ausbeul Gleithammer Satz or a finishing hammer to remove any remaining high spots.
Benefits of using Ausbeulstation for car dent repair
There are 5 key benefits of using an ausbeulstation for modern vehicle maintenance:
-
Vehicle value retention is maximized because the original factory paint is preserved through Dellenentfernung durch Klebetechnik (glue-based dent removal).
-
Minimal invasiveness guarantee ensures that the structural integrity of the panel remains intact.
-
Certified technician network support is easier to achieve when using standardized equipment like the DENTSTATION 39.04.
-
Aluminum panel expertise is enhanced through dedicated tools like the SPEEDLINER ALU PRO, which handles the unique thermal properties of aluminum.
-
Insurance claim assistance becomes more straightforward as these stations provide consistent, high-quality results that meet industry standards.
Cost comparison between traditional methods and Ausbeulstation
Ausbeulstation repairs are generally 30% to 50% cheaper than traditional methods for small to medium dents. While a traditional fahrzeugreparatur (vehicle repair) might cost 500 € (approx. 530 $) due to painting and filler materials, a Smart Repair approach at an ausbeulstation can often be completed for 150 € to 250 € (approx. 160 $to 265$). Savings are achieved because there is no need to purchase expensive automotive paints or spend hours on drying times. For businesses, the ROI (Return on Investment) is fast because the SPEEDLINER PRO 400 + ARCPULL 200 allows for more vehicle turnovers per day.
Impact on the environment
The environmental impact of an ausbeulstation is significantly lower than conventional bodywork. Because the technology focuses on lackierfreies Ausbeulen, it eliminates the emission of Volatile Organic Compounds (VOCs) typically found in automotive paints and thinners. Furthermore, it reduces waste by repairing existing panels rather than replacing them with new plastic or metal parts. Choosing eco-friendly dent removal helps shops meet sustainability goals while reducing the hazardous waste footprint of the autowerkstatt.
Future potential and expansion of Ausbeulstation technology
The future potential of ausbeulstation technology lies in increased automation and integration with digital diagnostics. Platforms like Youtube and Youku already host countless tutorials from GYS CHINA and GYS GERMANY, showing how DENTSTATION ARC PULL 200 + PRO 400 units are evolving to handle thinner, high-strength steels. As electric vehicles (EVs) become more common, the need for precise, low-heat repair methods will drive the expansion of DENTSTATION EXPERT 230 systems across global markets.
Conclusion
The ausbeulstation is the definitive future of Karosserie Reparatur, offering a professional, efficient, and clean alternative to traditional bodywork. By utilizing specialized components like the SPEEDLINER EXPERT or the DENTSTATION ARC PULL, workshops can provide lackschadenfreie Ausbeulstation Reparatur that ensures vehicle value retention. Whether dealing with hagelschadenreparatur (hail damage repair) or parkdellen (parking dents), these stations integrate the best of Smart Repair and invisible repair technology. As we move forward, the adoption of units like the SPEEDLINER PREMIUM PRO 230 will continue to define excellence in the karosseriewerkstatt.
Technology
How to Create Makeup Transformation Posters with AI
Why makeup transformation posters are popular
-
Dramatic beauty transformations
-
Artistic makeup inspired by fantasies or fashion
-
Creative color schemes or lighting
-
Beauty portraits used in campaigns
Turning beauty ideas into visual concepts
-
Day-to-night beauty transformations from natural to glamorous
-
Fashion or editorial makeup inspired by fashion trends
-
Fantasy or inspirational beauty inspired by myths or movies
-
Colorful artistic face designs used for social media content

Designing posters for beauty campaigns and social media
-
Promotion of makeup tutorials on Instagram
-
Beauty campaign posters
-
Makeup workshop or masterclass posters
-
Beauty portfolio posters
Exploring creative beauty characters
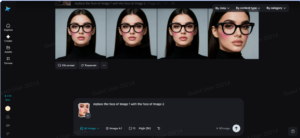
Turning beauty transformations into posters with Dreamina
Step 1: Upload your image
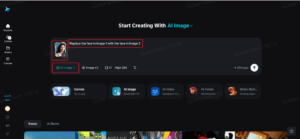
Step 2: Customize and create
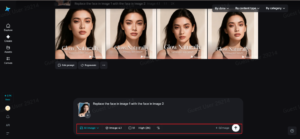
Step 3: Download your deepfake image
Preparing the image for better visual quality
The process of making transformation posters visually striking
-
The use of bold light effects that emphasize facial features
-
The use of bright colors that represent makeup artistry
-
The use of proper composition to ensure the face is emphasized

Using transformation posters to build a beauty brand
-
Beauty social media campaigns
-
Beauty online portfolios
-
Promotional materials for workshops
-
Visual branding for makeup artists
Final thoughts: Creating makeup transformation posters with Dreamina
-

 Entertainment2 months ago
Entertainment2 months agoهنتاوي.com Hub for Trending Arabic Content and Digital Stories
-
Others2 months ago
Insert Han Reference Here: The Veilside Fortune RX-7
-
Others2 months ago
Pure Rally Bred: Law’s Lancer Evolution VI Tommi Makinen Edition
-
Others2 months ago
Humble Celebrity: Ramon Bautista’s Lancer “Evo III”
-

 Technology2 months ago
Technology2 months agoEporer Revolutionize Industries with Innovation and Efficiency
-

 Business2 months ago
Business2 months agoPLG Supplies Trusted Industrial and Commercial Supply Partner
-

 Gaming2 months ago
Gaming2 months agoGarforfans Ultimate Fan Hub for Gaming and Pop Culture
-
Others2 months ago
Everyday Show Car: Henry’s Jaos Complete Edition Toyota FJ Cruiser
