Technology
PPPoE High-Speed Internet Setup & Benefits

PPPoE (Point-to-Point Protocol over Ethernet) is a networking protocol that enables Internet Service Providers to manage multiple users over a shared Ethernet connection through authentication, session control, and IP assignment. Commonly used in DSL and some fiber networks, it creates a secure, session-based connection requiring a username and password. While it offers strong user control, billing accuracy, and basic security, it also introduces minor overhead and configuration complexity. Compared to DHCP, PPPoE provides better user-level management but is less seamless for end users.
The main benefits of using this protocol include enhanced security through mandatory logins and the ability for providers to track data usage accurately. It simplifies the process of assigning IP addresses to customers while ensuring that only authorized users access the network. Most home and small business DSL connections rely on this system to maintain a stable link to the web. The core components involve a client, usually a router or computer, and a server located at the ISP’s central office.
What is PPPoE?
PPPoE is a specification for connecting multiple computer users on an Ethernet local area network to a remote site through common customer premises equipment. This term describes a method of encapsulating PPP frames inside Ethernet frames. To understand it, you must look at its two parents: PPP and Ethernet. PPP is an old standard used for direct connections between two nodes, often associated with dial-up modems. Ethernet is the standard for local area networks. When high-speed internet like DSL arrived, providers needed a way to use the ease of Ethernet while keeping the control features of PPP.
This protocol allows an ISP to provide individual accounts to many users sharing a physical network. It functions at the network layer and the data link layer of the OSI model. When you use this protocol, your computer or router sends a request to the ISP’s server. This request asks for a connection. Once the server sees the request, it asks for a username and password. This process is called authentication. It ensures that you are a paying customer before letting you access the wider internet.
In the early days of the internet, dial-up was the king. You used a phone line and a modem. The modem dialed a number and established a point-to-point link. As technology moved to DSL and cable, the physical connection changed to Ethernet. However, Ethernet by itself does not have a native way to check who is logging in or how much data they use. It treats everyone on the wire as part of the same big group. ISPs hated this because they couldn’t bill people easily or shut off specific users. By wrapping PPP inside Ethernet, they gained the best of both worlds.
The technical name for this is encapsulation. Imagine you have a letter, which is your data. You put that letter in a small envelope, which is the PPP frame. Then, you put that small envelope into a larger shipping box, which is the Ethernet frame. The shipping box gets the letter through the local neighborhood wires. Once it reaches the ISP, they open the box, check the small envelope for your ID, and then send the letter on its way. This double-layer approach is why you often have to enter a password into your router settings during setup.
Today, this protocol remains a staple for many broadband providers globally. While newer technologies like DHCP are becoming more common in fiber and cable setups, millions of DSL lines still use this method. It provides a level of control that simple Ethernet connections lack. It manages the session from the moment you turn on your router until you turn it off. This session-based nature is a hallmark of the protocol, distinguishing it from “always-on” styles of networking where the connection is implicit rather than explicitly negotiated.
You Might Also Like: Labarty
What is It used for?
The primary use of this protocol is to facilitate communication between a provider and a subscriber. Most people interact with it when setting up a new home internet connection. If your ISP gives you a username and a password that ends in something like “@isp.com,” you are likely using this protocol. It serves as a digital gatekeeper. Without it, the ISP would struggle to know which customer is which on a shared line. This is especially true in apartment buildings or neighborhoods where many people connect to the same local hub.
Authentication is the most common function. When you log in, the ISP identifies your account. This allows them to apply specific rules to your connection. For example, if you pay for a 100 Mbps plan, the ISP uses the session established by this protocol to cap your speed at that limit. If you miss a payment, they can simply deny your login attempt. This is much easier than sending a technician to physically disconnect a wire. It provides a software-based management system for hardware-based connections.
Another major use is IP address management. There are a limited number of IPv4 addresses in the world. ISPs do not want to give you a permanent address if you aren’t using it. With this protocol, the ISP assigns you an IP address only when your router starts a session. When you turn your router off, that IP address goes back into a pool for someone else to use. This dynamic allocation helps the ISP save money and resources. It also provides a small layer of privacy for the user, as your IP address might change every few days.
Data tracking is also a key usage. Because every bit of data goes through a specific session tied to your ID, the ISP can count exactly how many gigabytes you download. In regions where data caps are common, this protocol is the tool that makes those caps possible. It generates logs of when you connected and when you disconnected. For businesses, this can be useful for auditing network usage. For the provider, it is a vital part of the billing infrastructure that ensures they get paid for the service they provide.
Finally, it is used to provide security for the connection. Because it supports various encryption and authentication protocols like PAP and CHAP, it is harder for a neighbor to “sniff” your data directly off the wire compared to a wide-open Ethernet network. While it is not a replacement for a VPN or modern web encryption, it adds an initial layer of verification. It ensures that the person using the bandwidth is the person authorized to do so. This protects both the ISP from theft of service and the user from certain types of local network interference.
How does It work?
The process begins with two distinct stages: the Discovery stage and the Session stage. During the Discovery stage, your computer or router acts as the client. It needs to find a server, known as an Access Concentrator, on the ISP’s network. Since Ethernet is a broadcast medium, the client sends out a special packet to everyone on the local segment. This is called a PADI packet, or PPPoE Active Discovery Initiation. It is basically the client shouting, “Is there a server out here that I can talk to?”
Once the ISP’s server hears this shout, it responds with a PADO packet, which stands for PPPoE Active Discovery Offer. This is the server saying, “I am here, and I can give you a connection.” Often, there might be multiple servers that hear the initial shout, so the client might receive several offers. The client then chooses the best offer and sends a PADR packet, or PPPoE Active Discovery Request. This confirms to the chosen server that the client wants to start a formal link. The server finishes the handshake by sending a PADS packet, which provides a unique Session ID.
Now that the Discovery stage is over, the Session stage begins. This is where the PPP part of the name comes into play. The client and server move into a point-to-point communication mode using the Session ID they just created. The first task in this stage is Link Control Protocol (LCP) negotiation. This is where the two sides agree on how they will talk. They decide on things like the maximum packet size and whether they will use compression. If they can’t agree on these basic rules, the connection fails immediately.
After the rules are set, the next step is authentication. This is the part users are most familiar with. The client sends the username and password to the server. The server checks its database to see if the credentials are valid. If they are, the server moves to the Network Control Protocol (LCP) phase. Here, the ISP provides the client with an IP address. It also gives the client the addresses of DNS servers, which are needed to translate website names into numbers. Once this is done, the connection is fully active and the user can browse the web.
The connection stays alive as long as data is moving or until one side decides to close it. To keep things stable, the client and server occasionally send “Keep-Alive” packets to each other. This is like checking a pulse to make sure the other side is still there. If the server doesn’t hear from the client for a while, it will close the session to free up resources. When you want to disconnect, your router sends a PADT packet, or PPPoE Active Discovery Terminate. This tells the server the session is over, and the IP address can be returned to the pool.
Common Applications of PPPoE
The most common application of this protocol is in Digital Subscriber Line (DSL) internet services. For decades, DSL has been a primary way for homes to get online. Since DSL uses existing telephone lines, ISPs needed a way to make those lines act like modern network connections. This protocol was the perfect solution. It allowed them to treat a simple copper pair as a secure, authenticated network port. Even as fiber-to-the-home (FTTH) grows, many providers still use this protocol on their fiber networks to maintain their existing billing and management systems.
Another application is in multi-tenant buildings like apartments or hotels. In these settings, the building might have one large fiber connection. The management then distributes that connection to each unit via Ethernet cables in the walls. By using this protocol, they can give each tenant a specific login. This prevents one tenant from using all the bandwidth or accessing another tenant’s files. It turns a shared physical wire into a series of private, virtual tunnels. This is a cost-effective way to manage high-density internet access without complex hardware for every room.
Small businesses often use this protocol for their wide area network (WAN) connections. Because it supports various authentication methods, it allows businesses to secure their branch office connections. A company can set up a router in a remote office that automatically logs into the main corporate network or a specific ISP gateway. It provides a level of consistency for IT departments. They can use the same setup scripts and credentials across many different locations, regardless of the local physical infrastructure, as long as the provider supports the protocol.
Wireless Internet Service Providers (WISPs) also rely heavily on this method. WISPs provide internet to rural areas using radio waves. Since the air is a shared medium, security is a major concern. Anyone with the right antenna could theoretically hop onto the network. By requiring a login via this protocol, the WISP ensures that only paying customers can actually move data through the radio link. It also helps the WISP manage the limited bandwidth available in wireless spectrums by capping individual users based on their login profiles.
Finally, some older Virtual Private Network (VPN) setups utilized variations of this logic. While modern VPNs like OpenVPN or WireGuard have largely taken over, the concept of “tunneling” one protocol inside another remains a foundational idea in networking. Understanding how this protocol encapsulates data helps engineers build more complex systems. It serves as a teaching tool for how the layers of the OSI model interact. It proves that you can take an old, reliable method of communication and wrap it in a new one to solve modern problems.
Benefits and drawbacks of PPPoE
One of the biggest benefits is the control it gives to the service provider. For the company selling the internet, this protocol is a dream. It allows for precise authentication, which means they can ensure that only people who pay for the service get it. It also allows for detailed logging. If there is a legal issue or a technical problem, the ISP has a record of exactly when a specific user was online and what IP address they were using. This accountability is vital for large-scale operations.
For the user, a benefit is the relative security compared to an open network. Because your router must negotiate a session, it is harder for someone to simply plug into your wire and start using your internet. The session-based nature also means that your IP address is likely to change. While this can be a drawback for some, for the average user, it adds a small layer of anonymity. It makes it slightly harder for websites to track you over long periods based solely on your IP address.
However, there are significant drawbacks. The most notable is the overhead. Because you are wrapping a PPP frame inside an Ethernet frame, you lose some space for actual data. This affects the Maximum Transmission Unit (MTU). A standard Ethernet frame is 1500 bytes. This protocol takes up 8 bytes of that space for its own headers. This leaves only 1492 bytes for your data. If your equipment is not configured correctly to handle this smaller size, you may experience slow speeds, broken websites, or issues with online gaming and VPNs.
Complexity is another downside. Setting up this protocol is more difficult than using a simple DHCP connection. A user has to know their username and password and enter them into the router’s configuration page. If the user forgets their password or types it in wrong, the internet simply won’t work. For many people, this is a point of frustration. It adds a “moving part” to the connection process that can break. If the ISP’s authentication server goes down, no one can get online, even if the physical wires are perfectly fine.
There is also the issue of “always-on” connectivity. While modern routers handle the login process automatically, the connection is technically not always active. It has to be established. In some older or poorly configured systems, this can lead to a slight delay when you first try to use the internet after a period of inactivity. Additionally, some routers struggle to maintain the session, leading to frequent “dropouts” where the router has to re-authenticate. This is less common with modern hardware, but it remains a potential point of failure that doesn’t exist in simpler protocols.
PPPoE vs. DHCP
The main rival to this protocol in modern networking is DHCP, or Dynamic Host Configuration Protocol. DHCP is much simpler for the end user. With DHCP, you just plug your router into the wall, and the ISP automatically gives it an IP address and all the settings it needs. There is no username and no password. It is a “plug and play” experience. This is why most cable and fiber providers have moved toward DHCP. It reduces customer support calls because there are fewer things for the user to get wrong.
The difference lies in how they handle the connection. This protocol is session-oriented. It creates a virtual tunnel between your router and the ISP. DHCP is connectionless. It simply broadcasts a request for an IP address, and a server gives it one for a set period, known as a “lease.” Because DHCP doesn’t have the 8-byte overhead of PPP, it allows for a full 1500-byte MTU. This makes it slightly more efficient and less likely to cause issues with data fragmentation or packet loss in complex network setups.
From the ISP’s perspective, DHCP is harder to use for individual user management. Since there is no login, the ISP has to identify you based on the physical ID of your modem or the specific port you are plugged into. If you move your modem to a neighbor’s house, the ISP has to do extra work to figure out who is using the bandwidth. This protocol makes that easy because your login works wherever you are on their network. However, most modern ISPs have found ways to use DHCP while still keeping tight control over their customers.
Security also differs between the two. This protocol requires a password, which feels more secure. However, that password is often sent using relatively weak encryption. DHCP relies on the physical security of the line. If someone can tap into your fiber line, they can get an IP address via DHCP just as easily as they could try to steal your password. For most home users, the security difference is negligible. The real security comes from the firewall on your router and the encryption used on the websites you visit.
You Might Also Like: Asiaks
Pros and Cons of PPPoE
When evaluating this protocol, it is helpful to look at a list of its strengths and weaknesses. On the pro side, it is a very mature technology. Because it has been around for decades, almost every router on the market supports it. You won’t find a home gateway that doesn’t have a setting for it. This universal support makes it a safe choice for ISPs who want to ensure their service works with a wide variety of customer-owned equipment. It is a known quantity in the world of networking.
Another pro is the ability to offer “tiered” services. Because the session is tied to a user account, the ISP can easily change your service level on the fly. If you decide to upgrade your speed, they just update a setting in their central database. The next time your router logs in, it gets the new speed. This is much cleaner than having to reset hardware or reconfigure physical ports. It also makes it easy for ISPs to provide “pay-as-you-go” or temporary internet access, such as at a convention or a short-term rental.
On the con side, the “MTU issue” is a persistent headache for network administrators. Many people don’t realize that their internet is slow because of a packet size mismatch. When a packet is too big for the 1492-byte limit, it has to be broken into two pieces. This is called fragmentation. It slows down the network and increases the load on the router. In some cases, if a website is set up to block certain types of control messages, the fragmented packets might be dropped entirely, causing the website to simply never load.
Lastly, there is the issue of troubleshooting. When your internet goes down with this protocol, there are more places to look for the problem. Is it a physical line fault? Is it a wrong password? and is the ISP’s authentication server down? With a simpler protocol, the list of suspects is shorter. For the average person who just wants to watch a movie, having to log into a router to check a “PPP Status” page is not an ideal experience. It adds a layer of technicality that many people find intimidating.
FAQs
Do I need to set up PPPoE on my computer?
In most cases, no. Your router handles the connection for you. You enter the credentials into the router’s settings, and it manages the login. Your computer, phone, and tablet then connect to the router via standard Wi-Fi or Ethernet. However, if you are plugging your computer directly into a DSL modem that doesn’t have a built-in router, you might need to set up a “Broadband Connection” in your operating system’s network settings using the provided username and password.
Is PPPoE slower than other types of internet?
Technically, it has a tiny bit more overhead, which means a very small percentage of your bandwidth is used for the protocol itself rather than your data. However, in real-world usage, you won’t notice a speed difference compared to DHCP, provided your MTU settings are correct. The speed of your internet is determined much more by your ISP’s service plan and the quality of your physical line than by the protocol used to log in.
What happens if I lose my PPPoE password?
If you lose your password, your router will not be able to establish a session, and you will not have internet access. You will need to contact your ISP’s customer support. They can usually reset the password for you or remind you what it is. It is a good idea to write this information down and keep it in a safe place, or keep the original welcome letter provided by your ISP when you first signed up for the service.
Can I use a VPN with a PPPoE connection?
Yes, you can. However, this is where the MTU issues mentioned earlier often crop up. Since both this protocol and a VPN add headers to your data, the available space for your actual data gets even smaller. If you find your VPN is slow or won’t connect, you might need to lower the MTU setting in your router or your VPN software to something like 1400 or 1452 to ensure the packets fit through the “tunnel” without being broken apart.
Why is my ISP still using PPPoE in 2026?
Many ISPs stick with it because their entire billing and management system is built around it. Replacing it would require a massive and expensive overhaul of their backend software. If it isn’t broken, they often see no reason to spend millions of dollars to change it. Additionally, for DSL providers, it remains the most efficient way to manage individual subscribers over old copper phone lines. It is a reliable, proven method that does exactly what they need it to do.
Technology
Rblwal A Unique Digital Brand Concept
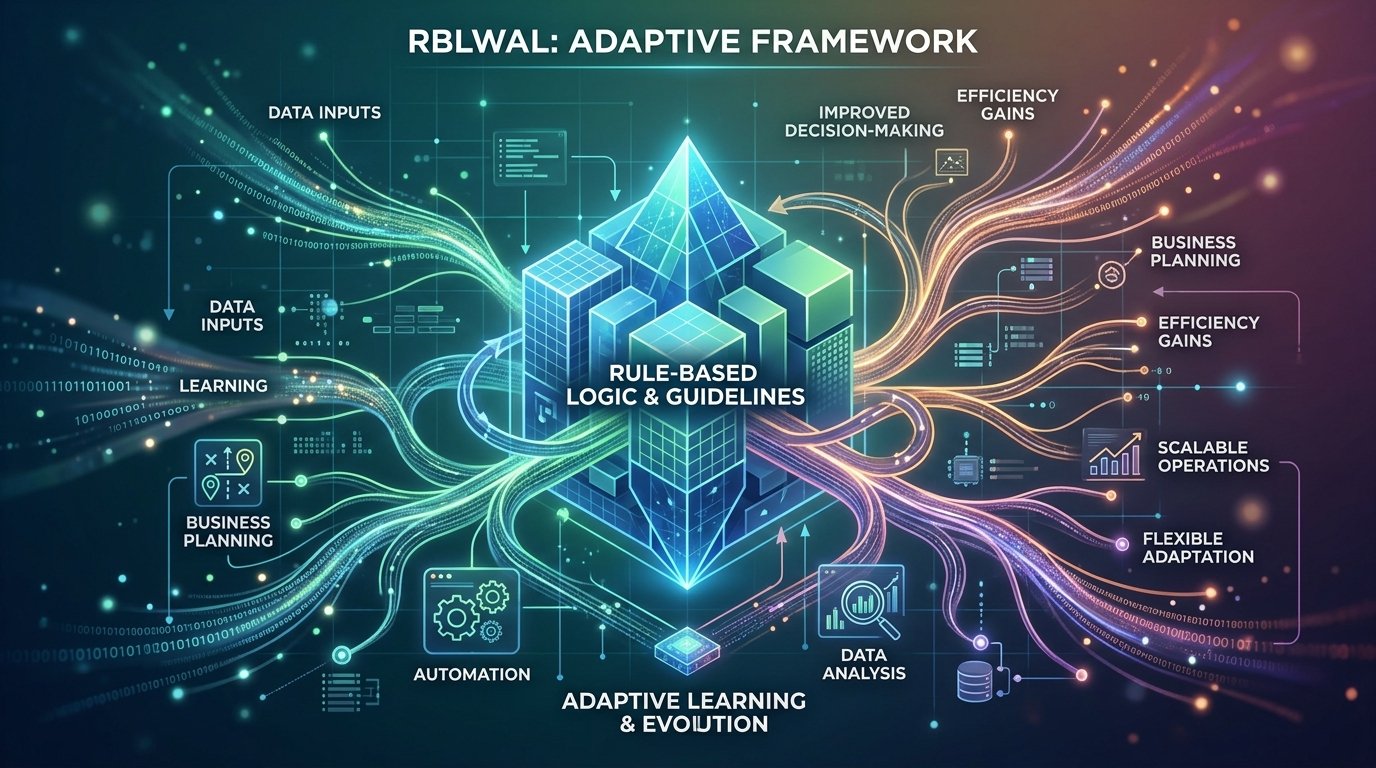
There are 5 main benefits of using Rblwal, including increased accuracy, faster workflow speeds, consistent output quality, operational flexibility, and long-term scalability. Its primary applications span multiple sectors such as business planning, automated technology, and data analysis. The Rblwal framework consists of 4 primary components: a Rule-Based System (RBS), Logical Thinking (LT), Adaptive Learning (AL), and Workflow Connection (WC).
What Is Rblwal?
Rblwal is a system that uses rules and learning to improve results over time. It is not a single software or product but a digital methodology used to manage tasks through structured logic. The term is often broken down into a common full form to explain its core functions.
Common Full Form of RBLWAL
The full form of RBLWAL (RBLWAL) provides a clear look at how the system operates:
-
R: Rule
-
B: Based
-
L: Logic
-
W: With
-
A: Adaptive
-
L: Learning
This structure ensures that every action starts with a rule but ends with a lesson learned, making the system smarter with each use.
You Might Also Like: Sodiceram
The Power of Unique Digital Branding
Rblwal serves as a strong keyword for digital branding because it is unique and easy to remember. In a crowded online space, a short and distinct name helps a business stand out.
There are 4 reasons why Rblwal is an effective brand name:
-
Unique word: It has low competition in search engine results.
-
Memorability: The phonetic structure is simple for users to recall.
-
Versatility: It can represent an app, a consulting firm, or a tech product.
-
Global appeal: The name does not have restrictive cultural meanings, making it safe for international use.
Possible Uses of Rblwal
Rblwal is used in 4 major areas: business, technology, data management, and personal productivity. Because the system is flexible, it adapts to different professional needs.
Business and Technology Applications
-
Planning: Create step-by-step business strategies that adjust as market data changes.
-
Automation: Power smart tools that handle repetitive tasks using fixed rules.
-
Risk Control: Identify potential errors by comparing current data against established logical patterns.
-
Data Analysis: Use the adaptive learning component to predict future performance trends.
Rblwal in the Modern Technology Landscape
It fits into the modern technology landscape by acting as a bridge between simple automation and advanced Artificial Intelligence (AI). While basic tools only follow “If-Then” rules, it includes a learning layer that modifies those rules.
In current tech environments, Rblwal helps manage NFC (Near Field Communication) systems, social media analytics, and e-commerce growth strategies. For example, a digital marketing tool might use Rblwal logic to set a rule for posting times and then adapt that rule based on when followers are most active.
Building a Strong Identity
Building a strong identity with it requires a focus on consistency and customization. To establish a brand around this concept, you must define the specific values the name represents for your audience.
Identity building involves 3 specific steps:
-
Define the Logic: Clearly state what “rules” your brand follows.
-
Customization: Use unique logos and color palettes to make the name visually distinct.
-
Engagement: Use the adaptive learning aspect to listen to customer feedback and refine your brand voice.
Real Case Study: From Name to Brand
A real case study of it shows how a keyword transforms into a service model. Consider a digital agency that adopted the Rblwal framework to manage SEO (Search Engine Optimization) for clients.
The agency set 10 initial rules for content creation, including 9th-grade reading levels and specific keyword densities. As they tracked search rankings, the “Adaptive Learning” part of the Rblwal system signaled that longer sentences performed better for certain niches. The agency updated their rules immediately. This resulted in a 15% increase in organic traffic within three months because the system was built to change, not stay rigid.
Challenges Facing Rblwal
There are 4 main challenges facing it, including the lack of a fixed official definition and the need for high-quality data. Because it is a growing concept, users may encounter obstacles during implementation.
| Challenge | Impact on User |
| No Fixed Definition | Can cause confusion for new adopters. |
| Data Dependency | Requires accurate data to learn effectively. |
| Complexity | Setting up the initial logic can be time-consuming. |
| Resource Costs | Needs time and professional expertise to maintain. |
Future Potential of Rblwal
The future potential of it is high in the fields of AI, business automation, and digital asset management. As technology becomes more autonomous, systems that can learn and self-correct will become the standard.
Growth is expected in 3 specific areas:
-
Smart Business Tools: Apps that manage schedules and budgets automatically.
-
Digital Branding: More companies using unique, short keywords to capture niche markets.
-
Predictive Analytics: Software that uses Rblwal logic to forecast stock trends or market shifts.
You Might Also Like: Charfen.co.uk
FAQs
What is rblwal?
Rblwal is a system that combines fixed logical rules with adaptive learning. It is used to make processes more efficient by learning from past results.
Is rblwal a real company?
No, rblwal is currently a digital concept and a branding keyword. Many different businesses use it as a name for their products or service models.
How does the adaptive learning part work?
Adaptive learning works by checking the results of a task and updating the original rules to improve the next outcome. It creates a repeating cycle of growth.
Where can I apply Rblwal?
You can apply Rblwal in business planning, technology automation, and personal goal tracking. Use it anywhere you want to combine structure with the ability to improve.
Technology
NS Crewcall Guide to Use It for Your Next Project

NS Crewcall (NSC) is a centralized platform for managing workforce logistics, connecting project managers with freelancers for industries like railways and media production. It streamlines hiring, scheduling, and communication through a unified dashboard, mobile app, and secure database. By enabling real-time collaboration, automated updates, and budget tracking, NSC improves efficiency, reduces delays, and simplifies project management for complex teams.
NS Crewcall (NSC) is a centralized logistics and workforce management platform used to coordinate transportation personnel and production teams. NS Crewcall works as a digital hub that connects project managers with skilled freelancers while automating scheduling and communication. By utilizing this system, organizations increase operational efficiency and improve resource allocation. The platform offers 4 primary benefits: streamlined hiring, real-time collaboration, centralized project tracking, and transparent budgeting. Main applications of NSC include managing railway crew assignments, commercial film productions, and corporate video projects. The system consists of 3 main components, which are the user dashboard, the mobile application, and the secure mainframe database.
How It Works
NS Crewcall (NSC) functions as an intuitive interface that bridges the gap between production needs and available talent. To use the system, managers create detailed project listings that define specific roles and technical requirements.
There are 3 main steps in the NSC workflow:
-
Project Listing: Users post opportunities within specific categories including cinematographers, sound engineers, and equipment operators.
-
Freelancer Application: Qualified professionals browse active listings and submit digital portfolios through the platform.
-
Direct Communication: The system facilitates instant messaging between parties to ensure alignment on project goals.
The platform processes updates in real time. If a schedule changes, the system immediately notifies all assigned members to maintain synchronization.
Benefits of Using It for Your Production
Using it provides significant advantages for managing complex logistics and creative teams. There are 5 key benefits of using NS Crewcall for your production, including faster hiring cycles and better budget transparency.
-
Diverse Talent Pool: NSC provides access to a wide network of professionals with specialized skills.
-
Enhanced Collaboration: Built-in tools foster constant communication among team members.
-
Time Efficiency: The automated notification system reduces the time spent on manual follow-ups.
-
Centralized Tracking: Managers monitor project progress through a single dashboard.
-
Financial Control: Transparent pricing and budget tracking tools help keep expenses within set limits.
Finding and Hiring Freelancers on NS Crewcall
Finding the right freelancers on NS Crewcall (NSC) involves utilizing the platform’s advanced filtering and review systems. To find talent, start by defining the project scope and necessary expertise.
Once the project is live, you can filter candidates based on 3 criteria:
-
Experience Level: Filter by years in the industry or specific project types.
-
Location: Find local talent to reduce travel costs and logistics.
-
Skill Sets: Search for specific technical proficiencies such as 4K editing or railway safety certification.
Review candidate portfolios carefully and check ratings from previous clients. Engaging in direct conversation through the NSC messaging system helps determine if a freelancer fits the team culture before you make a formal commitment.
Managing Your Project on NS Crewcall
Managing your project on NS Crewcall (NSC) centralizes all administrative tasks into a single digital workspace. The intuitive dashboard allows you to organize schedules and track milestones without external spreadsheets.
To manage effectively, use the 3 primary management tools:
-
Scheduling Module: Set deadlines and reminders to prevent task delays.
-
Budget Monitor: Track expenses in real time to ensure financial compliance.
-
Feedback Mechanism: Gather insights from the crew during and after the project to improve future workflows.
Mobile access ensures that managers stay connected while on set or in the field. This portability allows for immediate adjustments to the plan if unexpected issues arise.
Tips for a Successful Project with NS Crewcall
To ensure success with NS Crewcall (NSC), prioritize clarity and consistent engagement with the platform. A structured approach leads to better results and higher-quality outputs.
There are 4 essential tips for project success:
-
Define Clear Objectives: Write specific project descriptions to attract the most relevant talent.
-
Maintain Open Dialogue: Perform regular check-ins with the crew through the built-in messaging features.
-
Set Realistic Timelines: Include buffer periods in the schedule to account for potential delays.
-
Engage the Community: Build a network of reliable contacts within the platform for future collaborations.
Regularly updating the project status keeps all stakeholders informed and reduces the need for repetitive status meetings.
FAQs
What is the NS Crewcall phone number?
The NS Crewcall phone number is the primary contact for technical support and crew inquiries, though users should check their specific regional portal for the most accurate local number.
How do I perform an NS Crewcall login?
To perform an NS Crewcall login, visit the official NSC portal (nscorp.com) and enter your authorized username and password.
Is there an NS Crewcall app for mobile?
Yes, the NS Crewcall app is available for iOS and Android devices. The mobile app allows crew members to view assignments and receive emergency alerts while traveling.
What should I do if I forget my NS Crewcall password?
Reset your password by clicking the “Forgot Password” link on the login page. Follow the prompts to verify your identity through your registered email or a One-Time Password (OTP).
Can I manage budgets through NS Crewcall?
Yes, you can manage budgets through the NSC dashboard. The system provides tools to track expenses and view transparent pricing for freelance services.
Technology
Bardid The Future of Creative Technology

Bardid is an AI-powered digital creativity platform that combines generative AI, Natural Language Processing (NLP), and intuitive design tools to streamline content creation. It helps users produce text, visuals, and videos efficiently while enhancing collaboration through real-time features. With benefits like increased productivity, cost efficiency, and accessibility, Bardid is transforming industries such as marketing, education, and web development. As AI technology evolves, Bardid is expected to play a key role in democratizing creative workflows worldwide.
In a fast-paced environment where digital innovation moves rapidly, Bardid is a dominant force shaping how people express digital creativity. This technology functions by integrating Artificial Intelligence (AI) and Natural Language Processing (NLP) to streamline content creation and design workflows. The main benefits of Bardid include increased productivity, cost efficiency, and accessibility for creators at all skill levels. Users apply Bardid to generate marketing materials, develop brand identities, and produce immersive media. The core components of the system involve an Intuitive Interface, Smart Automation, and Real-Time Collaboration tools.
What Is Bardid?
Bardid is a digital creativity platform that combines generative AI with intuitive design tools to simplify the creative process. This technology utilizes Large Language Models (LLMs) and Transformer Models to assist users in generating text, visuals, and videos. Unlike traditional software that requires extensive training, Bardid focuses on a user-friendly experience. It acts as a bridge between complex machine learning and artistic expression.
How It Is Transforming Digital Creativity
Bardid is changing the digital age by simplifying complex creative processes. Tasks like graphic design and content editing that previously required hours now take minutes. This shift allows a designer or creator to focus on storytelling rather than technical constraints.
Additionally, the platform improves teamwork through Real-Time Collaboration. Remote teams use integrated feedback systems to refine creative projects instantly. This reduces the time spent on back-and-forth communication and speeds up the delivery of digital content.
Key Features That Make Bardid Stand Out
There are 5 main features that define the Bardid experience:
-
Intuitive Interface: Provides an easy-to-use workspace that reduces the learning curve for beginners.
-
Smart Automation: Handles repetitive tasks to save time during the production of marketing materials.
-
Real-Time Collaboration: Allows multiple users to work on a single project simultaneously to improve efficiency.
-
Creative Templates: Offers pre-designed layouts for logos, website elements, and social media posts.
-
Cross-Platform Access: Enables users to access their work from various devices, ensuring flexibility for entrepreneurs.
Benefits of Bardid for Creative Professionals
There are 4 primary benefits for professionals using this technology:
-
Increased Productivity: Streamlined workflows allow for more output in less time.
-
Cost Efficiency: Reduces the need for expensive third-party professional services.
-
Accessibility: Adapts to the skill level of the user, whether they are a student or a senior professional.
-
Continuous Innovation: Regular updates keep users aligned with the latest trends in artificial intelligence.
Potential Applications for Bardid in Different Industries
Industries use it in various ways to improve their digital presence:
-
Digital Marketing: Influencers create eye-catching visuals and videos to engage audiences on social media.
-
Small Business: Startups build brand identities by creating logos and marketing materials without a large budget.
-
Education: Educators and students develop interactive learning materials to improve engagement in the classroom.
-
Web Development: Creators design website elements and layout mockups efficiently.
Tips to Maximize Your Bardid Experience
To get the best results from it, follow these 4 strategies:
-
Prioritize ideas first: Use the platform as a tool to support your original concepts.
-
Test automation features: Explore how smart automation can handle your most repetitive tasks.
-
Maintain consistency: Use the platform regularly to develop your skills and speed.
-
Monitor updates: Stay informed about new features in Transformer Models and NLP.
Challenges and Considerations with Bardid
While the Bardid AI platform is powerful, users must consider certain challenges. Over-reliance on automation can lead to a loss of the “human touch” in creative work. As more people use these digital solutions, standing out requires extra effort in original storytelling. Users should also be aware of the data analytics involved and ensure their creative processes remain unique.
Future of It and Its Impact on the Creative Industry
The future of it involves deeper integration with immersive media and Google AI developments. We can expect more sophisticated Generative AI that understands nuanced artistic requests. This evolution will likely lead to even more democratization in the creative industry, making high-level production available to everyone with a digital connection.
Frequently Asked Questions (FAQ)
Is Bardid suitable for beginners?
Yes, Bardid is suitable for beginners because it features an Intuitive Interface and guided workflows. These elements help new users create professional-grade visuals without prior technical expertise.
Does Bardid require a high-speed internet connection?
Yes, Bardid requires a stable internet connection because it operates as a cloud service. Most processing happens on remote servers using Deep Learning and neural networks.
Can Bardid generate videos?
Yes, Bardid can generate videos by using Generative AI models to compile clips and animations. Users often use these for social media and marketing materials.
How many languages does Bardid support?
Bardid supports over 40 languages for text generation and NLP tasks. This includes major global languages to help remote teams collaborate internationally.
-

 Entertainment4 months ago
Entertainment4 months agoهنتاوي.com Hub for Trending Arabic Content and Digital Stories
-
Others4 months ago
Insert Han Reference Here: The Veilside Fortune RX-7
-
Others4 months ago
Pure Rally Bred: Law’s Lancer Evolution VI Tommi Makinen Edition
-
Others4 months ago
Humble Celebrity: Ramon Bautista’s Lancer “Evo III”
-
Others4 months ago
Everyday Show Car: Henry’s Jaos Complete Edition Toyota FJ Cruiser
-

 Technology3 months ago
Technology3 months agoEporer Revolutionize Industries with Innovation and Efficiency
-
Others4 months ago
Infinite Power Fanfare: A Full Mugen Showcase In One EG Hatch
-

 Business4 months ago
Business4 months agoPLG Supplies Trusted Industrial and Commercial Supply Partner
